Cybersecurity Outsourcing

Things You Should Know About Cybersecurity Outsourcing In 2025 Are you looking for cybersecurity outsourcing? Do you want to perform cybersecurity outsourcing but don’t know how to get started? The pandemic was alarming not only for humankind but also for the cybersecurity world because it just fueled the fire back then. Millions of cybersecurity threats […]
Avalon Security

A Comprehensive Guide To Avalon Security Are you looking for a perfect yet comprehensive guide to get started on Avalon Security? Do you often face severe cyber attacks and don’t know where to start? You do, right? Don’t worry because Avalon security is the key to all your cybersecurity issues. Cyber threats are increasing each […]
SentinelOne Competitors

Top 5 SentinelOne Competitors That Will Blow Your Mind Are you looking for SentinelOne competitors that can make your life easy? Do you want an instant solution to all your cybersecurity issues? Then don’t worry; we’ve got you covered. SentinelOne is well known for its remarkable services in the past; however, clients are facing issues […]
Top 7 Best Qualys Alternatives That Will Blow Your Mind

Are you looking for the best Qualys alternatives in 2025? Or perhaps you’re looking for a company that provides similar services at lower rates? Then, you’ve landed on the right spot. Qualys is a popular vulnerability, patch and compliance management provider; however, it’s not suitable for everyone. The primary reason you should be looking out […]
Is Vumetric Cybersecurity Legit? A Comprehensive Guide

Are you considering Vumetric Cybersecurity for your organization’s protection? Or, perhaps you’re looking for the information and services Vumetric Cybersecurity provide. If yes, you’ve landed on the right page. An organization’s security balance is crucial. To maintain it, one must go through many procedures. A short mistake in a cybersecurity system can disrupt firewalls, and […]
A Comprehensive Guide to Android Penetration Testing
Do you know you’re under an online threat attack? What if you get to know that all your valuable sensitive information is seen and observed by others? Scary, isn’t it? The unsecured android applications can cause a serious threat on your privacy and security of your device. Majorly, it can cause a lot of commercial […]
Top 10 Fastest Growing Cybersecurity Companies in USA

Cybersecurity companies has evolved ever since the great yet drastic cyber security attack of the notoriously infamous Creeper and Reaper occurred in the 1970s which took the attention of people. A whopping amount of $185.70 billion is available in the cyber security market. World is interconnected today and with its multiple benefits, there are still […]
Cybersecurity and Cyberwar: What Everyone Needs To Know

If you are someone who knows about cybersecurity then you must have heard about the book “Cybersecurity and Cyberwar: What Everyone Needs to Know” at some point in your life. The book itself is the epitome of knowledge about the cyber world and how we are at cyberwars. It provides an intricate and dynamic field […]
Effective Strategies for Businesses to Stay Ahead of Cybersecurity Threats
As an organization, what is your biggest fear? A cybersecurity breach attack, isn’t it? We all know how crucial it is to maintain cybersecurity and how well you must maintain things to keep your sensitive data safe. While many companies and organizations pay a lot of attention to their cybersecurity system, others lack in a […]
Understanding the Connection Between Cybersecurity and the Internet of Things (IoT)
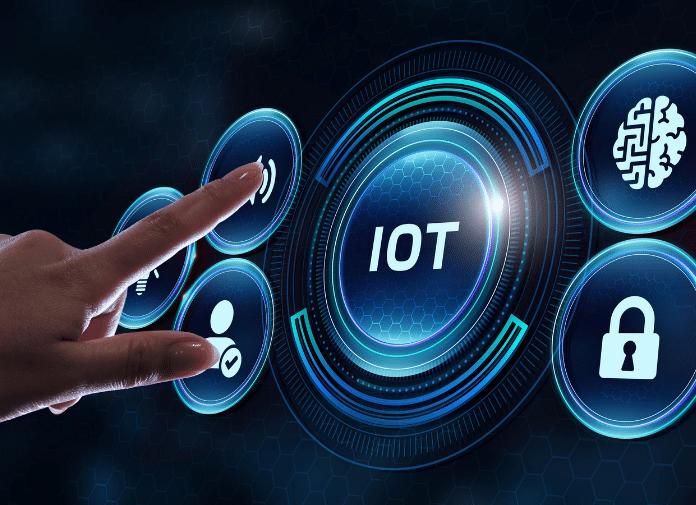
As Internet of Things (IoT) technology is becoming increasingly popular, it is a big challenge for organizations. Yes, you guessed it right, cybersecurity. Cybersecurity is used as a shield against cyberattacks and cybercrimes to prevent organizations from falling into a pit that leaves them in chaos. Similarly, the Internet of Things refers to everything interconnected […]
