Phishing Scam: Japanese Telecom Users’ Credentials Stolen by Fake Android Apps

Phishing is one of the most common cybercrimes affecting consumers and organizations all around the world. It is one of the most popular Internet scams.
End-Users To Be Verified At The Helpdesk To Prevent Social Engineering Cyber Attack

Multiple social engineering schemes are scattered across the internet; however, social engineering techniques might steal any user’s credentials.
Thousands Laid Low With Ransomware Attack On Hawaii Company

Ransomware attack on Hawaii company. Hawaii Payroll Services learned that unauthorized users had gained access to its computers and information.
Apple Issues A Warning On An Active Exploited Zero-Day Vulnerability On Macs

Apple has issued a security alert to iPhone and Mac customers, stating that it is aware of a zero-day vulnerability that is being actively exploited.
UK Armed Forces Declare Cyber As The Fifth Dimension Of Warfare

Cyberwarfare is not a computer-versus-computer fight but rather a much broader notion. It is an attempt to attack an opponent using cyberspace or other digital means.
Warning!!! Malicious Content Is Served Via Archive.Org

Professionals have recently found malevolent and violating content on Archive.org. Malicious content can be anywhere, but you just need to use the internet vigilantly to secure your data.
Incident Response And How To Best Handle It

do you know a well-defined incident response plan (IRP) enables you to identify, mitigate the damage, and lower the cost of a cyber assault!
API Keys Lead to Millions Lost in Cryptocurrencies

Stolen API Keys are one of the leading causes of huge financial losses in cryptocurrencies. Keeping them safe is critical to preventing losses.
Zero Day Attacks – Understanding how it works and Prevention Tips

To help protect from this, we may have multiple layers of protection in our system. This includes firewalls, scanners, encryption, next-gen security protocols, and all the other fancy names. Sure, these protection systems work and keep us away from everyday problems, however, these devices can still miss an Attack.
5 Common Cloud Security Threats and How to Mitigate Them
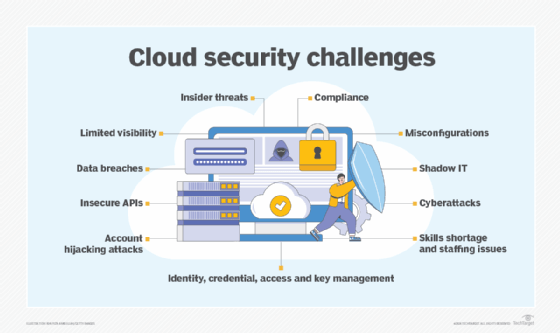
Cloud computing has provided businesses with the option to scale up the organization and introduce flexibility. But at the same time, it has exposed networks to increased data breaches and attacks. The attack on the network can result in a potential loss of information, time, and money. Hence, prevention is always better in this case.
