- Cyber Security Services
- SOC2 Certification
Critical Vulnerabilities Exposed? Schedule a Penetration Test Now.
Join our clientele’s community & secure your business today with RogueLogics

Identify, Exploit, Fix: Choose Your Penetration Testing Service
Take control with our customized penetration testing services. Our ethical hackers will identify weaknesses in your systems, safely exploit them to understand their potential impact, and provide a clear roadmap for fixing them before they can be used by malicious actors.

Secure Your Systems with Penetration Testing
Don’t be a sitting duck. Hackers are constantly searching for vulnerabilities in your systems. A penetration test, also known as pen testing, simulates a real-world attack, identifying security weaknesses before they can be exploited.
Our team of ethical hackers will put your systems to the test, uncovering vulnerabilities in your network, applications, and infrastructure. We’ll then provide a detailed report outlining the risks, potential impact, and clear steps to remediate the issues.

Simulate a Real Attack with Red Team Exercises
Go beyond traditional security testing. Red Team exercises simulate a real-world attack, deploying a team of ethical hackers to relentlessly probe your defenses, uncover hidden weaknesses, and expose potential breaches. This rigorous testing provides an unparalleled view of your security posture, helping you identify and address critical vulnerabilities before attackers do.
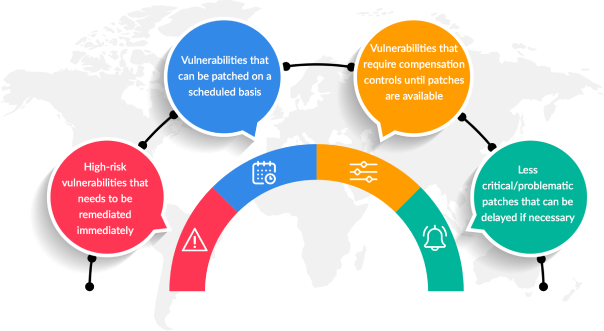
Vulnerability Assessment: Expose Your System's Weaknesses
Unlike a ticking time bomb, a vulnerability assessment can expose the weaknesses in your network, applications, and infrastructure before they can be exploited by attackers. It’s a comprehensive scan that acts like a security expert examining your system for cracks in the armor, proactively identifying and prioritizing vulnerabilities to give you peace of mind and ensure compliance with regulations.

Compliance & Confidence? Achieve Both with a Security Audit.
Uncover vulnerabilities, ensure compliance, and gain valuable insights to strengthen your security posture with a comprehensive security audit. Our experienced auditors will analyze your policies, controls, and procedures, assess your network and physical security, and test your incident response plan, providing a detailed report with actionable recommendations to reduce your risk of a breach.
Testimonials: Experience the Difference
Nothing completes the picture except real validation from real clients. See why our clients love us and why you need to engage us for your firm as well.
When our website got breached, we had no idea what to do. We were referred to Rogue Logics and we have not looked back since. Super friendly folks with superb security background.

Our lead developer just quit and we had a major release that needed to go out. Our frantic search lead us to this firm and I must say that what sets them apart from others is their can do attitude.

We had serious security flaws in our core codebase. After years of struggle with web app malfunctions, we finally reached out to Rogue Logics and our code is super secure now.

Let's Grow Together
Roguelogics.com empowers companies with cutting-edge cybersecurity solutions, including threat detection, risk assessment, and tailored strategies, ensuring robust security against emerging threats.
